Our Services
Explore our full range of services

Real-Time Threat Monitoring
Our 24/7 SOC leverages AI-driven analytics for continuous surveillance across networks, endpoints, and cloud environments. Detect anomalies in milliseconds and respond with automated playbooks tailored to your assets. Ensure zero downtime with proactive threat hunting rooted in regional intelligence.

Vulnerability Assessments
Comprehensive scans using advanced tools identify exploitable weaknesses before adversaries do. We prioritize findings by business impact, delivering remediation roadmaps with CVSS-aligned metrics. Achieve audit-ready compliance through iterative testing and false-positive elimination.
Customized Security Architecture
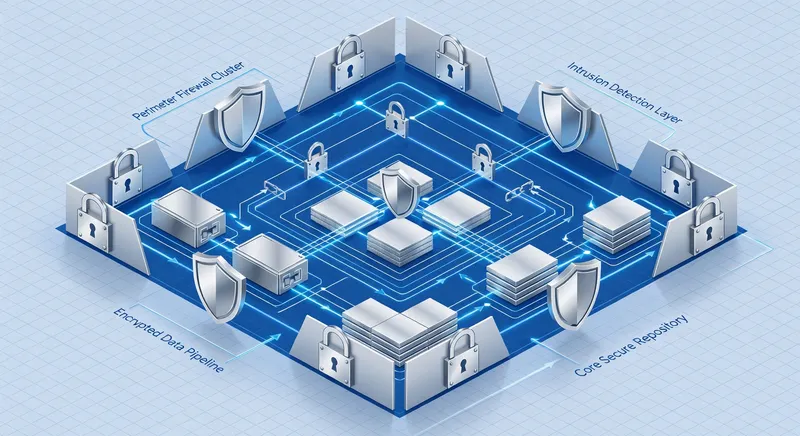
Design scalable, zero-trust architectures integrating on-prem, hybrid, and multi-cloud setups. Align with DSGVO and NIS2 directives while incorporating global best practices like SASE. Future-proof your infrastructure against quantum threats and supply chain risks.

Incident Response & Forensics
Rapid containment and eradication with certified IR specialists using memory forensics and timeline reconstruction. Minimize breach dwell time to under 24 hours via tabletop exercises and retainer-based readiness. Restore operations with post-incident hardening recommendations.

Compliance & Data Sovereignty Audits
Expert audits ensuring adherence to EU regulations like GDPR and eIDAS, blended with frameworks such as SOC 2. Map controls to regional sovereignty principles for cross-border operations. Provide gap analyses and certification pathways for sustained compliance.
Pricing Plans
Essential
- ✓ Basic Monitoring
- ✓ Monthly Vulnerability Scans
- ✓ Compliance Reports
Professional
- ✓ 24/7 SOC
- ✓ Custom Architecture Design
- ✓ Incident Response Retainer
- ✓ AI Threat Hunting
- ✓ Priority Support
Enterprise
- ✓ Full Suite
- ✓ Dedicated Team
- ✓ Quantum-Resistant Upgrades
- ✓ Custom Training
- ✓ SLA Guaranteed
Features
Automated Threat Intelligence
Real-time feeds fused with regional OSINT for predictive alerting.
Custom Playbook Orchestration
SOAR workflows tailored to your tech stack for instant response.
Risk Quantification Dashboard
Executive views with financial impact modeling and ROI metrics.
Sovereignty Compliance Engine
Automated checks against EU regs with audit trails.
Endpoint Behavioral Analytics
ML-driven detection of insider and advanced persistent threats.
API Security Posture
OWASP Top 10 scanning with runtime protection.